HIPAA Compliant vs HIPAA Convenient
Many telehealth companies are claiming to be HIPAA compliant and some of them are. However, some of these technologies and the manner in which they are used by HIPAA covered health care providers, may not fully comply with the requirements of the HIPAA Rules. The 2020 COVID-19 pandemic has allowed for relaxed, “good faith” style regulations that allow many telehealth platforms to claim to be HIPAA compliant, taking advantage of the flexible atmosphere.
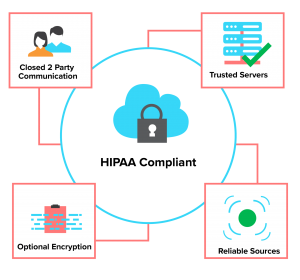
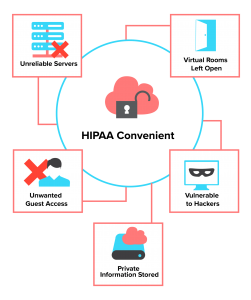
At surface level, it is difficult to tell the difference between the companies that are actually HIPAA-compliant and the ones that are considered “HIPAA convenient”. This article will tell you the signs to look out for to recognize the difference between the two, as well as the negative effects of selecting a HIPAA convenient platform.
Hacking Vulnerabilities
A truly HIPAA compliant telehealth platform will allow for only two parties to be able to engage in a conversation: the patient and the health care provider. They will also go to extreme lengths to ensure that the information stays between these two, and these two alone. This includes using trusted servers from reliable sources. Throughout the world, there are unreliable servers that many telehealth companies currently use for their platforms. These servers will open up virtual rooms to allow for a meeting to take place, and will often leave these “rooms” open for days or sometimes weeks, and multiple patients come in for sessions leaving them and the information stored vulnerable to hackers.
Zoombombing | verb
A series of pranks allowing for unwanted guests to gain access to meetings.
These always open sessions could also be hijacked by hackers in real-time. A well-known video conferencing company was recently sued as a series of pranks known as “zoombombing” allowed for unwanted guests to gain access to meetings and spew profanity as well as show explicit images. This company is one that claims to be HIPAA compliant. The best way to protect against similar results is to look into where the telehealth platform houses their servers, as well as how well they encrypt their information.
Information Encryption
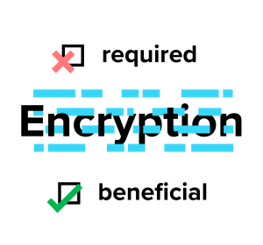
When it comes to securing Protected Health Information (PHI), there is no better way than end to end encryption. Data encryption translates data into another, coded form so that only people with access to a secret key (formally called a decryption key) or password can read it. Encryption is not explicitly required by HIPAA. This means that any company claiming to be HIPAA compliant doesn’t need to encrypt their platform in even the most basic manner. It is strongly suggested that anyone searching for a telehealth platform is able to fully understand the encryption measures taken before committing to a subscription.
The previously stated company, responsible for the zoombombing incident, had falsely advertised using encryption in their platform. They recently came out and said that the encryption was not currently possible in their platform. Instances like this just add to the difficulty of selecting a good platform, as the responsibility of thorough investigation is becoming more reliant on the consumer.
At VirtuSense, we know it isn’t enough to be “HIPAA convenient”. Patient privacy comes first, so we built VSTOne with end to end encryption, single-stream sessions, and two-factor authentication to ensure true HIPAA compliance and more.


